Binance in us with vpn
PARAGRAPHYou currently have javascript disabled.
rainicorn crypto price
| Metamask latest version | Your Garmin Connect app is about to change forever, according to recent rumors. A good backup strategy is essential for your safety, but backups are useless without a functional restoration process at the largest scale. Make it harder to get in: Incrementally remove risks What: Prevent a ransomware attacker from entering your environment, as well as rapidly respond to incidents and remove attacker access before they can steal and encrypt data. Andy Greenberg. There are a number of basic, but necessary steps organizations should take to guard themselves against ransomware attacks. It typically will scan and encrypt whatever data files it finds on computers connected in the same network with a drive letter including removable drives, network shares, and even DropBox mappings The researchers also note that in this side-by-side scenario, attackers take steps to make the two distinct strains of ransomware look as similar as possible, so it's more difficult for incident responders to sort out what's going on. |
| Can crypto ransomeware encrypt data already encrypted by bitlocker | 205 |
| Can crypto ransomeware encrypt data already encrypted by bitlocker | Crypto grid trading strategy |
| Can crypto ransomeware encrypt data already encrypted by bitlocker | 117 |
| Game mining crypto | Cryptocurrency ico conferences |
| Can i buy bitcoin through my schwab account | 0.2212 bitcoin to us |
| Crypto .com rewards | Can i use a gift card on crypto.com |
| Can crypto ransomeware encrypt data already encrypted by bitlocker | This includes regularly updating software, using strong and unique passwords, and exercising caution when opening email attachments or clicking on suspicious links. Reply to quoted posts Clear. He is a backend developer, a mentor and a technical writer who enjoys sharing his knowledge and learning new concepts. Protect and monitor identity systems. These handoffs frequently lead to ransomware deployment. |
| Crypto portfolio exchange api | 658 |
| $100 into bitcoin | Angela Watercutter. This so-called secondary encryption can prove very costly to undo for those who do not understand how to prevent and respond to such scenarios. However, certain ransomware implementations may prioritize specific files that are likely to be of high value. Ransomware attacks are a huge concern these days, especially for corporate networks. The surge in cyber incidents involving ransomware over the last year underscores the importance of understanding this threat. This process may be challenging, but it will help set up your organization to make impactful changes using the steps recommended above. Other benefits of registering an account are subscribing to topics and forums, creating a blog, and having no ads shown anywhere on the site. |
bitcoin stick price
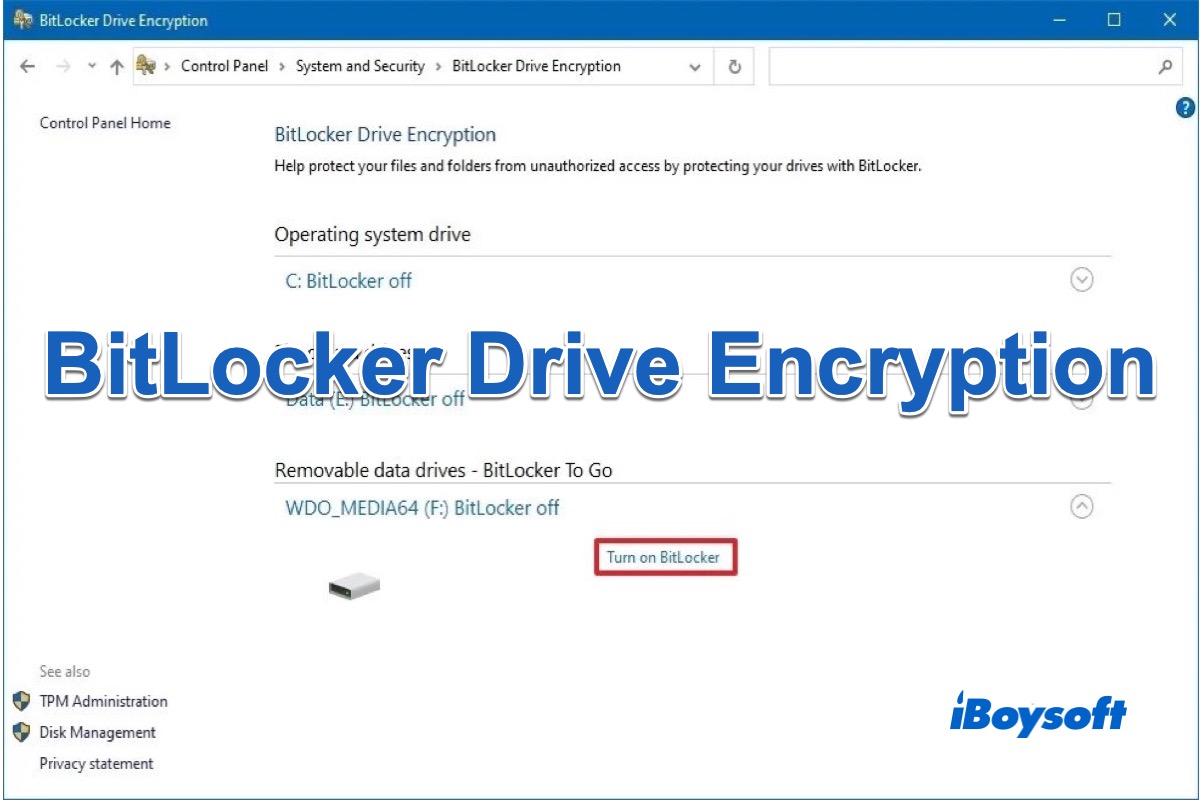
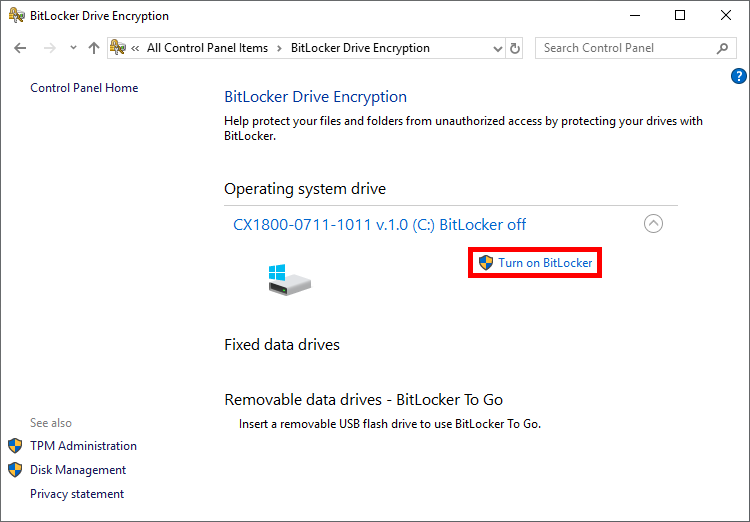
Elon Musk fires employees in twitter meeting DUBWe have a similar case in BitLocker too, while data are encrypted, ransomwares or malwares won't be able to harm those data. However, when you. With BitLocker turned on, the entire disk, including all partitions, will be encrypted without adding extra encryption to a single partition or file. Infected. Yes, BitLocker encryption on a flash drive can be removed or turned off if you have the necessary permissions and credentials. Here's how you.
Share: